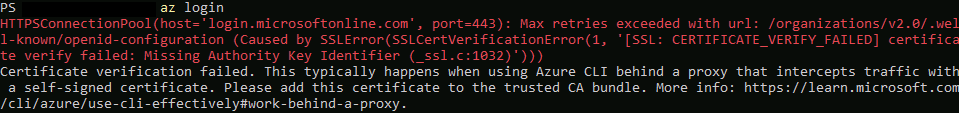
It looks like the more recent releases of Azure CLI are running off Python versions that enforce ‘Authority Key Identifier’ checks of the security certificates when connecting to Azure CLI (az login). You might see an error message similar to the below if bumping into this issue.
HTTPSConnectionPool(host=’login.microsoftonline.com’, port=443): Max retries exceeded with url: /organizations/v2.0/.well-known/openid-configuration (Caused by SSLError(SSLCertVerificationError(1, ‘[SSL: CERTIFICATE_VERIFY_FAILED] certificate verify failed: Missing Authority Key Identifier (_ssl.c:1032)’)))
Certificate verification failed. This typically happens when using Azure CLI behind a proxy that intercepts traffic with a self-signed certificate. Please add this certificate to the trusted CA bundle. More info: https://learn.microsoft.com/cli/azure/use-cli-effectively#work-behind-a-proxy.
The fun one here is you might be tempted to wonder if you’ve correctly imported your decryption certificates into the PowerShell module per the guide at https://learn.microsoft.com/en-gb/cli/azure/use-azure-cli-successfully-troubleshooting?view=azure-cli-latest#work-behind-a-proxy. However, if you look closely you’ll note that error is ‘Missing Authority Key Identifier‘ and not ‘self-signed certificate in certificate chain’.
It turns out that from Python 3.13 this Authority Key Identifier is now essential to allow the requests module to connect to addresses. The solution is pretty simple in running the command from https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA1Ki000000k9ddKAA on the CLI of the impacted firewalls – this allows the firewall to correctly handle this Authority Key Identifier field. Running the command did not impact any traffic flows or require any commits but your decryption certificate does require this Authority Key Identifier attribute to exist on the source certificate – in trying it out with a certificate generated from Active Directory Certificate Services it was present.
debug dataplane set ssl-decrypt akid-disable no
From the article it sounds like any firewall running 12.1 onwards will already have this value set making life easier (once there is a ‘stable’ release of 12.1 that is!).
Update 30/04/2026 – An account from the Palo Alto Networks forums suggests that even on a patched 12.1 firewall the command is required to resolve this one.